TLC, Inc.
13413
43RD Avenue SE
Mill
Creek, WA 98012
360-570-8787
December 4, 2010
Detective Reggie Dunn
Snohomish County
Police Department
Forensic
Investigations
230 Maple Avenue
Snohomish, WA 98290
You have asked TLC,
Inc. to examine items related to alleged evidence of counterfeiting. Your case has been assigned the designation
of SPD-07-0404.
On October 30, 2010,
Steve Hailey, representative of Snohomish County Police Department, turned over one hard drive to Pam Bolton of
TLC, Inc. The information below
describes how the items were marked when received and additional marking
information that was placed on them by TLC, Inc.:
|
As Received |
Marked by TLC, Inc. |
|
Forensic
image from a FUJITSU model MPE3102AT Serial
#: 01001158 Marked: SPD-07-0404 |
Case #:SPD-07-0404 |
Figure 1 Evidence
During the time that
TLC, Inc. had possession of the hard drive and chain of custody form, these
items were kept in a locked room located
on TLC, Inc.’s business premises.
The
instructions that Detective Dunn has given us related to the provided items are
as follows:
1.
Determine
if there is any evidence that could be related to counterfeiting activities.
The
images in this report have been formatted to fit the report.
All
exhibits are available on CD.
Definitions have been noted with
the designated color.
Manipulation of Computer
Date/Time
Information Relative to “How to” Counterfeit and Items
Needed To Counterfeit
Specific Examples of Counterfeiting
PROCEDURAL
OVERVIEW
My forensic workstation used to conduct
the analysis was scanned for viruses.
Diagnostics were run to assure that it was in good operational
condition. My workstation was not
connected to the Internet or any network.
·
The
hard drive copy was scanned for viruses, malicious programs and malware.
·
The
hard drive copy was compared against the vendor specifications in order to
account for all space on the drive, whether in use or not.
·
Information
present on the forensic image copy was indexed, and a listing of all files and
folders was created.
·
All
deleted
files that were recoverable were documented and restored.
·
Keyword
searches were conducted using keywords and phrases that are related to
counterfeiting.
·
Graphics
files were searched for and identified.
·
Web
pages or related content were searched for and extracted.
·
Internet history information was
extracted and examined to ascertain Internet usage, Internet searches, websites
accessed, and files downloaded/saved to the computer.
·
Searches
were conducted to locate activity related to chat rooms or the use of messaging
software.
·
Windows
registry
information was examined to locate information regarding Internet usage,
Internet searches, Websites accessed, and files downloaded/saved to the
computers.
·
The
Windows Recycle Bin contents were identified and examined.
·
Word
processing and other document/file types were searched for and extracted. All documents were checked for possible
encryption and/or password protection mechanisms.
·
Email
and email related artifacts were identified and examined.
·
Windows
event logs, software installation and other log types were identified and
examined.
FINDINGS
System
Information
|
Detail |
Value |
|
Windows
Version |
Microsoft
Windows XP |
|
Service
Pack |
SP1 |
|
Install
Date |
4/2/2007
09:27:37 UTC |
|
Registered
Owner |
Jack
Dickinson |
|
Computer
Name |
homeoffice |
|
Hostname |
homeoffice |
|
Current
IP Address |
192.168.0.1 |
|
DHCP Name Server |
68.87.69.146.68.87.85.98 |
|
Time Zone |
Pacific
Standard Time(UTC -0700) |
|
Last recorded
system shutdown |
4/4/2007
18:28:47 UTC |
User
Information
|
User Account |
Number of Logins |
Date of Last Login |
|
Administrator |
0 |
4/2/2007
2:17:24 UTC |
|
Guest |
0 |
4/2/2007 1:49:25 UTC |
|
Jack |
12 |
4/4/2007 18:26:16 UTC |
|
Molly |
4 |
4/4/2007 16:48:22 UTC |
|
|
|
|
|
Logon Account |
Utilized |
|
|
Ebay |
|
|
|
jdbackblack |
Ebay |
|
|
|
|
|
|
|
|
|
Devices
|
Fujitsu's
Desktop Model
# MPE3102AT |
|
|
** Seagate
5GB USB 2.0 Pocket
Hard Drive Model #:
ST65011USB |
|
|
** Hewlett
Packard Officejet 7410 All-in-one |
|
|
** Hewlett
Packard Photosmart M537 Digital Camera |
**There
appear to be these additional devices that were discovered in the registry that
were not provided for examination. I
believe that these devices may contain addition information relevant to this
investigation. I am providing a
declaration to that affect.
Miscellaneous
Findings
There were
indications of viruses or malware located on the image file. The virus found on the system was called
Cybesh.html. This virus does not have any effect on the evidence presented in
this report. More information on this virus can be found on the web page:
http://vil.nai.com/vil/content/v_118476.htm
|
VIRUS/MALWARE NAME |
LOCATION |
|
Trojan
download:JS\psyme.FL |
C:\Documents and
Settings\ Administrator\ Local Settings\ Temp\ ftktmp2428 |
|
Trojan
download:JS\psyme.FB |
C:\Documents and
Settings\ Administrator\ Local Settings\ Temp\ ftktmp2428 |
|
Exploit:win32/shellcode.gen!C |
C:\Documents and
Settings\ Administrator\ Local Settings\ Temp\ ftktmp2428 |
Manipulation of Computer Date/Time
·
The account of “Jack” shows a constant
changing of dates.
·
The last know shutdown time was April 4, 2007
·
The files in folder, “Vacation” shows the Created, Modified,
& Accessed dates. This
information Note: there are 2 masters.pdf due to the change of
dates.
·
The email message validated by receipt from gmail shows April
11, 2007
Information
Relative to “How to” Counterfeit and Items Needed To Counterfeit
The
account of “Jack” on this computer sought information relative to
counterfeiting, counterfeit detection and counterfeiting supplies:
·
conducted
several online searches
·
browsed
web pages
·
downloaded
and accessed documents
|
Exhibit |
Page |
Filename |
Definition |
|
|
|
|
|
|
B-1 |
12 |
001936[1].php |
Counterfeit
Detection (Part 1) |
|
B-2 |
13 |
2006-IUPR-17Aug_1131.pdf |
Printing
Technique Classification for Document Counterfeit Detection |
|
B-3 |
14 |
Counterfeiting.pdf |
Counterfeit
Identification – identification of counterfeit currency, credit cards,
traveler’s cheques and bank checks |
|
B-4 |
15 |
041011.Delp.forensics[1].htm |
Printer
forensics to aid homeland security, tracing conterfeiters |
|
B-5 |
16 |
Message0003 |
Email
researching printers |
|
B-6 |
17 |
02243.PDF |
Availability,
Performance and Cost of Recycled Paper |
|
B-7 |
18 |
search[3] |
Internet
search for “laser printer” and counterfeit |
|
B-8 |
19 |
eBayISAPI[2].htm |
Internet
search for “printers” |
|
B-9 |
19 |
074962003812_small1[1].jpg |
Book
on United States Paper Money |
|
B-10 |
20 |
laser_check_printers_and_counterfeit[3].htm |
Internet
search on “Laser Check Printers and Counterfeit Checks” |
|
B-11 |
21 |
counterfeit[1].htm |
Internet
search on “Desktop Counterfeiting Software” |
|
|
|
|
|
Specific
Examples of Counterfeiting
Money
A
directory named ‘Vacation” was located in a deleted partition on the
drive. This directory contained images
of bank checks along with images of United States Currency.
Note: There was a certain focus on the physical area of the money.
|
Exhibit |
Page |
Filename |
Definition |
|
|
|
|
|
|
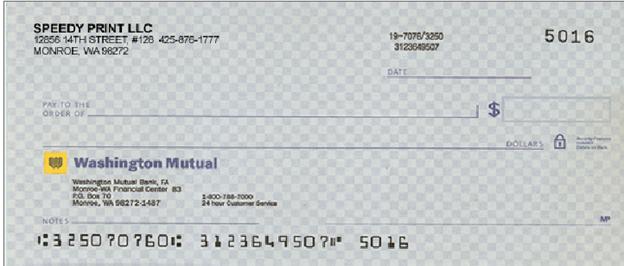
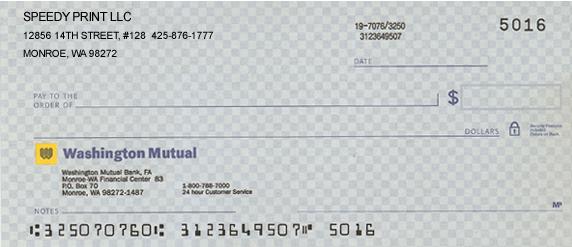
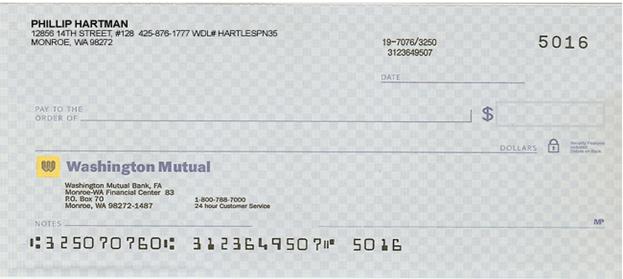
C-1 |
22 |
Vacation1.jpg |
Experimenting
with counterfeiting US paper currency |
|
C-2 |
22 |
Vacation2.jpg |
Experimenting
with counterfeiting US paper currency |
|
C-3 |
23 |
Vacation3.jpg |
Experimenting
with counterfeiting US paper currency |
|
C-4 |
23 |
Vacation4.jpg |
Experimenting
with counterfeiting US paper currency |
|
C-5 |
24 |
Vacation5.jpg |
Experimenting
with counterfeiting US paper currency |
|
C-6 |
24 |
Vacation6.jpg |
Experimenting
with counterfeiting US paper currency |
|
C-7 |
25 |
Vacation7.jpg |
Experimenting
with counterfeiting US paper currency |
|
|
|
|
|
The
different images of the checks appear to actually be of the same original check
that has been altered. One of the PSD
images of the check has user added notes stating “Best out of the bunch –
should pass for the Real McCoy”.
This same file shows to have a modified date after the creation date
which indicates at a minimum that this file was opened and saved after being
copied to this system
|
Exhibit |
Page |
Filename |
|
|
|
|
|
|
|
|
|
|
|
D-1 |
26 |
Try1 |
4/4/2007
8:25:50
AM |
4/2/2007
4:00:22
AM |
4/3/2007
11:00:00
PM |
|
D-2 |
26 |
Master |
4/4/2007
8:25:50
AM |
4/2/2007
4:05:40
AM |
4/3/2007
11:00:00
PM |
|
D-3 |
27 |
Try2 |
4/4/2007
8:25:50
AM |
4/2/2007
4:07:38
AM |
4/3/2007
11:00:00
PM |
|
D-4 |
27 |
Try3 |
4/4/2007
8:25:50
AM |
4/2/2007
4:14:18
AM |
4/3/2007
11:00:00
PM |
|
D-5 |
28 |
Master
2 |
4/4/2007
8:25:50
AM |
4/2/2007 4:14:30 AM |
4/3/2007
11:00:00
PM |
|
D-6 |
28 |
Master
3 |
4/4/2007 8:25:50 AM |
4/2/2007 4:14:30 AM |
4/3/2007
11:00:00
PM |
|
|
|
User
changed date (unable to determine sequence ) |
|||
|
D-7 |
29 |
Test |
4/4/2007 8:46:52 AM |
4/4/2007 8:46:46 AM |
4/3/2007 11:00:00 PM |
|
D-8 |
29 |
master |
4/4/2007 8:25:50 AM |
4/4/2007
8:48:06
AM |
4/3/2007
11:00:00
PM |
CONCLUSIONS
AND OPINIONS
Based on my computer forensic
experience, knowledge of computers and related technology, and analysis of the
evidence in this case, I believe that any competent computer forensic examiner
would agree with my conclusions and opinions that:
1.
In
my opinion, the manipulation of time and dates in an attempt to hide
information. This also included many
deleted files.
2.
Evidence
shows that the user “Jack” did extensive research for information which related
to counterfeiting, counterfeit detection, viable printers for counterfeiting,
and types of paper utilized.
3.
The person using the account of “Jack” accessed Adobe Photoshop,
which was utilized as image manipulation software to change the US paper
currency. The image format, PSD, is a
proprietary format of Photoshop.
4.
The
checks in evidence provide a result that the initial check was counterfeited.
.
I certify that the foregoing is true and correct to
the best of my knowledge, on a more probable than not basis.
_____________________________________ ________________________
Pamela A Bolton Date
EXHIBITS
Exhibit A-1
|
Last recorded
system shutdown |
4/4/2007
18:28:47 UTC |
Exhibit
shows time of last recorded proper shutdown.
The following information shows the system was used after this,
indicative a user made date/time change.
Exhibit A-2
File: Vacation1.jpg
Full Path: Dickinson\DeletedPart_2001\DATA-FAT32\Vacation\Vacation1.jpg
Created: 4/4/2007 9:25:48 AM
Modified: 2/8/2004 7:02:46 PM
Accessed: 4/4/2007 12:00:00 AM
File: Vacation2.jpg
Full Path:
Dickinson\DeletedPart_2001\DATA-FAT32\Vacation\Vacation2.jpg
Created: 4/4/2007 9:25:50 AM
Modified: 2/8/2004 7:02:44 PM
Accessed: 4/4/2007 12:00:00 AM
File: Vacation3.jpg
Full Path: Dickinson\DeletedPart_2001\DATA-FAT32\Vacation\Vacation3.jpg
Created: 4/4/2007 9:25:50 AM
Modified: 2/8/2004 7:15:30 PM
Accessed: 4/4/2007 12:00:00 AM
File: Vacation4.jpg
Full Path: Dickinson\DeletedPart_2001\DATA-FAT32\Vacation\Vacation4.jpg
Created: 4/4/2007 9:25:50 AM
Modified: 2/8/2004 7:02:46 PM
Accessed: 4/4/2007 12:00:00 AM
File:
Vacation5.jpg
Full
Path: Dickinson\DeletedPart_2001\DATA-FAT32\Vacation\Vacation5.jpg
Created: 4/4/2007 9:25:50 AM
Modified: 2/8/2004 7:14:52 PM
Accessed: 4/4/2007 12:00:00 AM
File:
Vacation6.jpg
Full
Path: Dickinson\DeletedPart_2001\DATA-FAT32\Vacation\Vacation6.jpg
Created: 4/4/2007 9:25:50 AM
Modified: 2/8/2004 7:02:44 PM
Accessed: 4/4/2007 12:00:00 AM
File:
Vacation7.jpg
Full
Path: Dickinson\DeletedPart_2001\DATA-FAT32\Vacation\Vacation7.jpg
Created: 4/4/2007 9:25:50 AM
Modified: 2/8/2004 7:02:48 PM
Accessed: 4/4/2007 12:00:00 AM
Exhibit A-3
Email,
message 003 – 4/11/2007
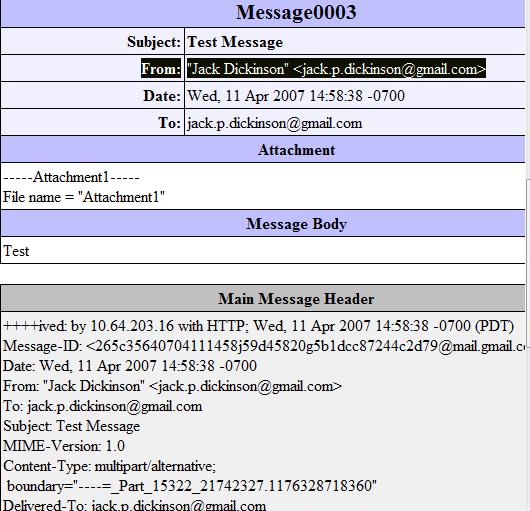
Exhibit B-1
File: 001936[1].php
Full Path: Part_1\NONAME-NTFS\Documents and
Settings\Jack\Local Settings\Temporary Internet Files\ Content.IE5\1C8Z29EL\001936[1].php
Created: 4/2/2007 3:16:44 AM
Modified: 4/2/2007 3:16:45 AM
Accessed: 4/2/2007 3:16:45 AM
Physical Size: 62,227 bytes
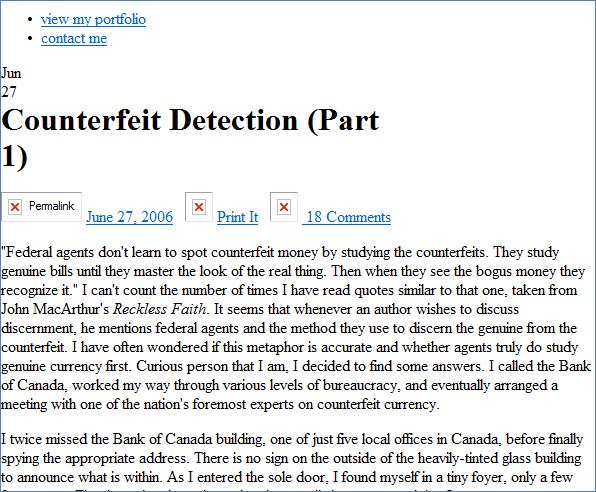
Exhibit B-2
File: 2006-IUPR-17Aug_1131.pdf
Full Path:
Dickinson\DeletedPart_2001\DATA-FAT32\2006-IUPR-17Aug_1131.pdf
Created: 4/2/2007 3:14:58 AM
Modified: 4/2/2007 3:15:00 AM
Accessed: 4/4/2007 12:00:00 AM
Physical Size: 1,663,463
Exhibit B-3
File: Counterfeiting.pdf
Full Path:
Dickinson\DeletedPart_2001\DATA-FAT32\Counterfeiting.pdf
Created: 4/2/2007 3:17:44 AM
Modified: 4/2/2007 3:17:46 AM
Accessed: 4/4/2007 12:00:00 AM
Physical Size: 62,912
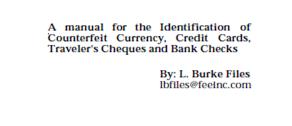
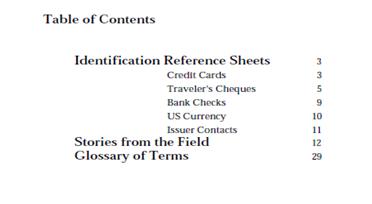
Exhibit B-4
File Name: 041011.Delp.forensics[1].htm
Full Path: Part_1\NONAME-NTFS\Documents
and Settings\Jack\Local Settings\
Temporary Internet
Files\Content.IE5\DS8DJ4ZH\041011.Delp.forensics[1].htm
Created: 4/2/2007 3:06:32 AM
Modified: 4/2/2007
3:06:32 AM
Accessed: 4/2/2007
3:06:32 AM
Exhibit B-5
File Name Message0003
Full Path: Part_1\NONAME-NTFS\Documents
and Settings\Jack\
LocalSettings\Application Data\Identities\
{EDBEA923-F071-4DC0-8D6F-4863CDFB453D}\Microsoft\Outlook
Express\
Deleted Items.dbx>>Message0003
Date: Wed,
11 Apr 2007 14:58:38 -0700
User: "Jack
Dickinson" <jack.p.dickinson@gmail.com> jack.p.dickinson@gmail.com
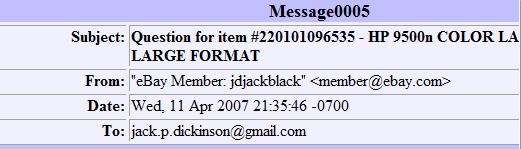
Exhibit B-6
File
Name: 02243.PDF
Full Path: DeletedPart_2001\DATA-FAT32\02243.PDF
Created: 4/2/2007
3:21:52 AM
Modified: 4/2/2007 3:21:58 AM
Accessed: 4/4/2007 12:00:00 AM
Exhibit B-7
File Name: search[3]
Full Path: Part_1\NONAME-NTFS\Documents
and Settings\Jack\
Local Settings\Temporary Internet
Files\Content.IE5\KLYVGTIV\search[3]
Created: 4/2/2007
3:12:46 AM
Modified: 4/2/2007
3:12:47 AM
Accessed 4/2/2007
3:12:47 AM
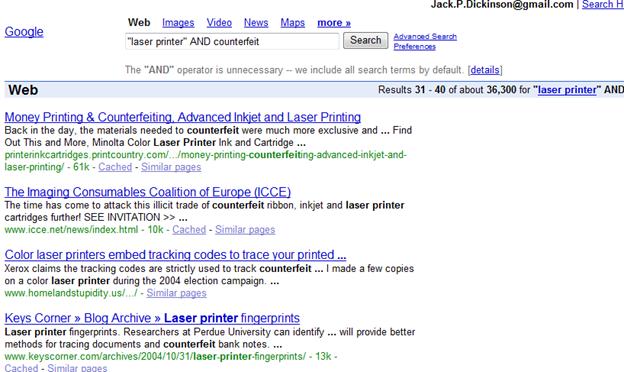
Exhibit B-8
File:
eBayISAPI[2].htm
Full Path: Dickinson\Part_1\NONAME-NTFS\Documents
and Settings\Jack\Local Settings\Temporary Internet
Files\Content.IE5\1C8Z29EL\eBayISAPI[2].htm
Created: 4/4/2007 9:37:10 AM
Modified: 4/4/2007 9:37:10 AM
Accessed: 4/4/2007 9:37:10 AM
Physical Size: 21,496
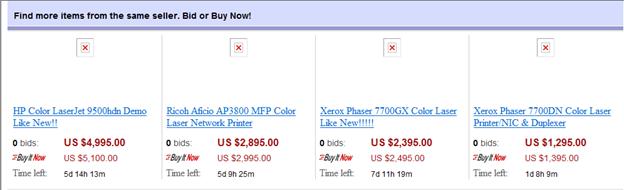
Exhibit B-9
File: 074962003812_small1[1].jpg
Full Path: Part_1\NONAME-NTFS\Documents and
Settings\Jack\Local Settings\Temporary Internet
Files\Content.IE5\1C8Z29EL\074962003812_small1[1].jpg
Created: 4/2/2007 3:26:15 AM
Modified: 4/2/2007 3:26:15 AM
Accessed: 4/2/2007 3:26:15 AM
Physical Size: 6,358 bytes

Exhibit B-10
File:
laser_check_printers_and_counterfeit[3].htm
Full Path: Part_1\NONAME-NTFS\Documents and
Settings\Jack\Local Settings\Temporary Internet
Files\Content.IE5\1C8Z29EL\laser_check_printers_and_counterfeit[3].htm
Created: 4/2/2007 3:27:17 AM
Modified: 4/2/2007 3:27:17 AM
Accessed: 4/2/2007 3:27:17 AM
Physical Size: 42,300 bytes
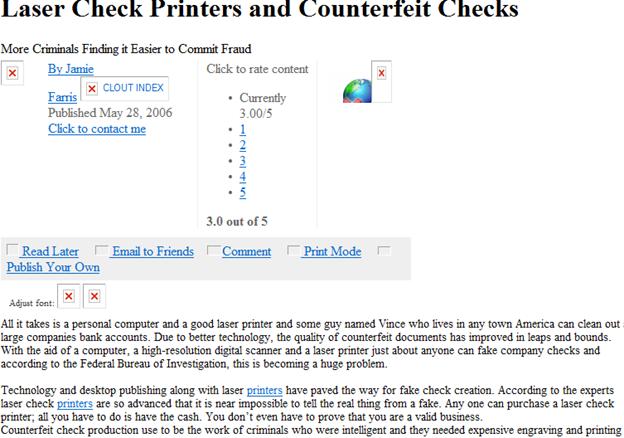
Exhibit B-11
File: counterfeit[1].htm
Full
Path: Part_1\NONAME-NTFS\Documents
and Settings\Jack\Local Settings\Temporary Internet
Files\Content.IE5\KLYVGTIV\counterfeit[1].htm
Created: 4/2/2007 3:14:18 AM
Modified: 4/2/2007 3:14:18 AM
Accessed: 4/2/2007 3:14:18 AM
Physical Size: 1,927 bytes
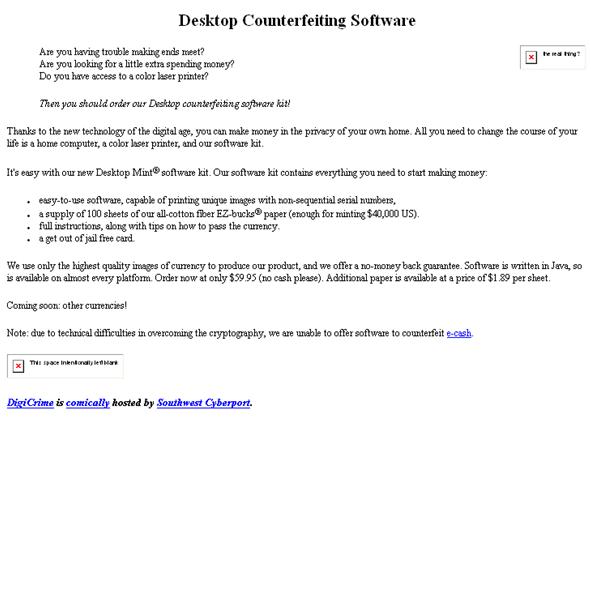
Exhibit C-1
File: Vacation1.jpg
Full Path: DeletedPart_2001\DATA-FAT32\Vacation\Vacation1.jpg
Created: 4/4/2007 9:25:48 AM
Modified: 2/8/2004 7:02:46 PM
Accessed: 4/4/2007 12:00:00 AM
Physical Size: 81,413 bytes

Exhibit C-2
File: Vacation2.jpg
Full Path:
DeletedPart_2001\DATA-FAT32\Vacation\Vacation2.jpg
Created: 4/4/2007 9:25:50 AM
Modified: 2/8/2004 7:02:44 PM
Accessed: 4/4/2007 12:00:00 AM
Physical Size: 404,010 bytes

Exhibit C-3
File: Vacation3.jpg
Full Path: DeletedPart_2001\DATA-FAT32\Vacation\Vacation3.jpg
Created: 4/4/2007 9:25:50 AM
Modified: 2/8/2004 7:15:30 PM
Accessed: 4/4/2007 12:00:00 AM
Physical Size: 292,698 bytes
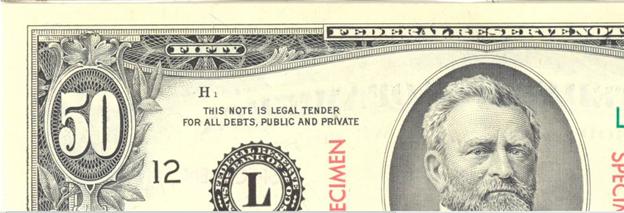
Exhibit C-4
File: Vacation4.jpg
Full Path: DeletedPart_2001\DATA-FAT32\Vacation\Vacation4.jpg
Created: 4/4/2007 9:25:50 AM
Modified: 2/8/2004 7:02:46 PM
Accessed: 4/4/2007 12:00:00 AM
Physical Size: 95,962 bytes
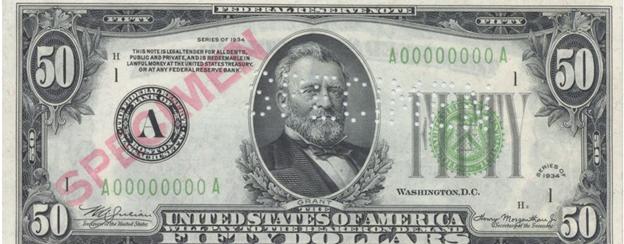
Exhibit C-5
File: Vacation5.jpg
Full Path: DeletedPart_2001\DATA-FAT32\Vacation\Vacation5.jpg
Created: 4/4/2007 9:25:50 AM
Modified: 2/8/2004 7:14:52 PM
Accessed: 4/4/2007 12:00:00 AM
Physical Size: 290,074 bytes

Exhibit C-6
File: Vacation6.jpg
Full Path: DeletedPart_2001\DATA-FAT32\Vacation\Vacation6.jpg
Created: 4/4/2007 9:25:50 AM
Modified: 2/8/2004 7:02:44 PM
Accessed: 4/4/2007 12:00:00 AM
Physical Size: 381,181 bytes

Exhibit C-7
File: Vacation7.jpg
Full Path: DeletedPart_2001\DATA-FAT32\Vacation\Vacation7.jpg
Created: 4/4/2007 9:25:50 AM
Modified: 2/8/2004 7:02:48 PM
Accessed: 4/4/2007 12:00:00 AM
Physical Size: 411,053 bytes
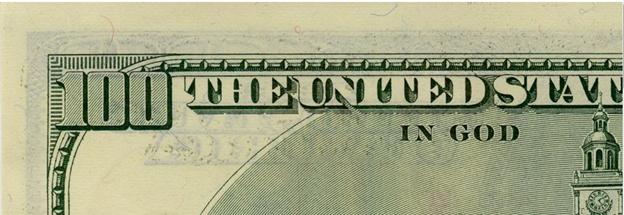
Exhibit D-1
File:
Master.psd
Full Path: DeletedPart_2001\DATA-FAT32\Vacation\Master.psd
Created: 4/4/2007 9:25:50
AM
Modified: 4/2/2007 5:05:40 AM
Accessed: 4/4/2007 12:00:00 AM
Physical Size: 2,732,966 bytes

Exhibit D-2
File: Master.psd
Full Path:
DeletedPart_2001\DATA-FAT32\Vacation\Master.psd
Created: 4/4/2007 9:25:50 AM
Modified:
4/4/2007 9:48:06 AM
Accessed: 4/4/2007 12:00:00 AM
Physical Size: 2,732,882 bytes
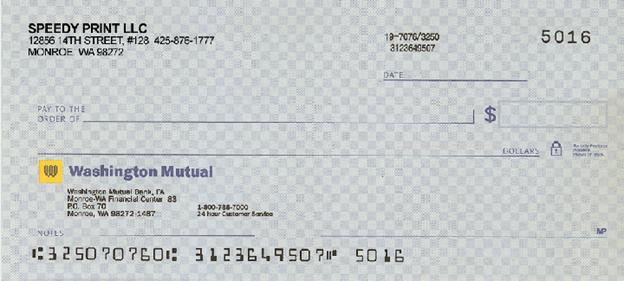
Exhibit D-3
File: Master2.psd
Full Path: DeletedPart_2001\DATA-FAT32\Vacation\Master2.psd
Created: 4/4/2007 9:25:50 AM
Modified:
4/2/2007 5:14:30 AM
Accessed: 4/4/2007 12:00:00 AM
Physical Size: 936,876 bytes
Exhibit
D-4
File:
Master3.psd
Full
Path: DeletedPart_2001\DATA-FAT32\Vacation\Master3.psd
Created: 4/4/2007 9:25:50 AM
Modified:
4/2/2007 5:14:28 AM
Accessed: 4/4/2007 12:00:00 AM
Physical Size: 1,256,200 bytes
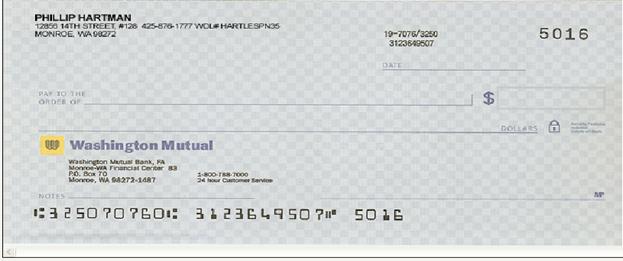
Exhibit D-5
File:
Test .jpg
Full
Path: DeletedPart_2001\DATA-FAT32\Vacation\Test.jpg
Created: 4/4/2007 9:46:46 AM
Modified:
4/4/2007 9:46:52 AM
Accessed: 4/4/2007 12:00:00 AM
Physical Size: 130,494 bytes
Exhibit
D-6
File: Try1.jpg
Full Path:
DeletedPart_2001\DATA-FAT32\Vacation\Try1.jpg
Created: 4/4/2007 9:25:50 AM
Modified: 4/2/2007 5:00:22 AM
Accessed: 4/4/2007 12:00:00 AM
Physical Size: 462,799 bytes
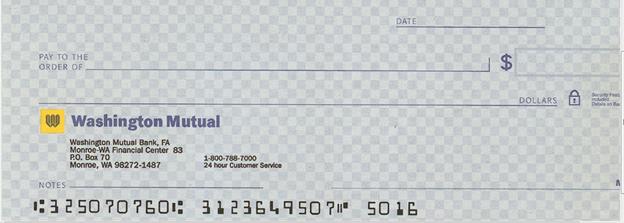
Exhibit D-7
File: Try2.jpg
Full Path:
DeletedPart_2001\DATA-FAT32\Vacation\Try2.jpg
Created: 4/4/2007 9:25:50 AM
Modified:
4/2/2007 5:07:38 AM
Accessed: 4/4/2007 12:00:00 AM
Physical Size: 139,816 bytes
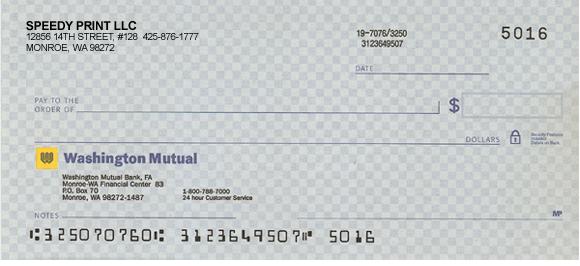
Exhibit D-8
File: Try3.jpg
Full Path: DeletedPart_2001\DATA-FAT32\Vacation\Try3.jpg
Created: 4/4/2007 9:25:50 AM
Modified: 4/2/2007 5:14:18 AM
Accessed: 4/4/2007 12:00:00 AM
Physical Size: 156,963 bytes
DEFINITIONS
Counterfeiting
Counterfeiting is
when a person is involved in the making of copies or imitations of items that
look strikingly like the real thing.
Deleted Files
When a file is
deleted in Windows, the entire file is not erased, it is simply marked as
“deleted” by the operating system. As a “deleted” file, it is no longer visible
to the end user, and the space it takes up on the hard drive is considered “unallocated.”
In order to truly delete a file, rendering it unrecoverable, the file must be
overwritten. This can be accomplished using tools designed to securely erase
files.
Internet History
Internet History is
information on Websites/Web pages and other content that was accessed, searches
conducted via search engines, as well as information on Web browser cookies.
Cookies are sent from Web sites typically to track site visitor activity.
Registry
The Windows registry
is a database which stores settings and options for Microsoft Windows. The
registry can record and store devices connected to the system, searches
conducted while accessing the Web, as well as information typed by the user
into Web-based forms. Information on files saved and opened by a particular
user can be found as well.